Power, Hidden Networks, and the Future of Democratic Governance
Introduction: The Gap Between Appearance and Reality in Government
Many countries hold regular elections, experience frequent leadership turnover, and have parliamentary legislatures. At first glance, this seems like normal democratic life. Yet some things stay the same, no matter the election outcome. Foreign policy often follows the same path under very different regimes. Even when ruling parties change, military budgets rise or remain high. Intelligence programs and security measures persist through liberal, conservative, or centrist administrations.
Different researchers refer to the deep state as the gap between visible politics and the decisions of permanent institutions, which are often unnoticed. In a 2025 review article in Public Administration Review, 64 publications (2009-2024) were reviewed, and the discussion of the deep state is present in political science, history, international relations, and public administration. Nevertheless, the article also observes that a deeper definition and use of the concept of deep state are also subject to dispute, as the term appears in serious scholarship and in the polemics of the day.
The phrase “deep state” in this article refers to groups of unelected actors who make and shape public policy. These include intelligence services, military commanders, senior civil servants, and allied commercial interests. They operate with varying levels of transparency and are rarely subject to electoral accountability or openness. Political scientist Patrick H. O’Neil describes the deep state as guided by a “logic of tutelage.” These actors claim to protect the nation from dangers that elected politicians cannot handle.
First, they trace the history of the deep state idea and its main components. Second, they discuss the actual operations of a deep-state system, using examples from Turkey, Pakistan, Egypt, the United States, and Russia. Third, they discuss their interactions with international partners, electronic surveillance, and private military and intelligence firms. Lastly, they assess the dangers and benefits of such enshrined power for democracy and reforms to enhance accountability. It aims to provide students and readers with a real picture of contemporary power without rejecting the deep state conception and applying it to all political phenomena.
Where Did the Idea Come From? The Historical Origins of the Deep State
Power Behind the Throne: Older Forms of Hidden Influence
The notion that true power lies behind nominal masters is prehistoric. Empires of the past had to be guided by unknowns. Medieval courts had informants and spies. They provided secrets and influenced decisions. In Rome, strong families influenced the Senate through silent persuasion and backdoor deals. They used these methods rather than open deliberation. These arrangements used hidden actors and informal networks. However, they were less organized and permanent than what many researchers now call the deep state.
Turkey and the Birth of the Term.
Building on these older forms of hidden influence, the concept of the deep state emerged in Turkey, taking on modern terminology.
The term deep state is a modern term derived from the Turkish language “Derin Devlet”. Historian Ryan Gingeras employs it to refer to a system of parallel rule in which informal actors are significant and influential in shaping state policy. The term became common in Turkey following a car accident on 3 November 1996 just outside the town of Susurlak in the northwest of the state. In the accident, a black Mercedes collided with a truck, where three out of four occupants of the car did not survive. Among the victims was a senior police officer, Abdullah Çatlı, a far-right militant, wanted by Interpol on a false passport, and his partner, a former beauty queen. Only one survived (Sedat Bucak), who was a member of parliament and a leader of the state-supported village guard militia. Many Turkish citizens saw the crash as proof that political figures, security forces, and criminal groups were working together.
The incident is known as the Susurluk Affair. It attracted the notice of a web of military personnel, spies, and nationalist paramilitaries like the Grey Wolves and criminal gangs utilized in the struggle against Kurdish rebels in the 1980s and 1990s. Scholars have suggested that this network can be traced back to the final years of the Ottoman Empire. In that time, secret military organizations were created to support the central authority. These structures were not dismantled clearly. Instead, they were rebuilt under new names when Turkey became a republic.
Authorities attempted to dismantle these networks through the Ergenekon trials of the late 2000s. Hundreds of military officers, journalists, and academicians were convicted of plotting a coup. A lot of those convictions were reversed. Analysts observe that the deep state in Turkey did not fade away in this period. It changed shape. To them, a system previously associated with the Kemalist and secular military elites was reconstructed by the Justice and Development Party (AKP) of President Recep Tayyip Erdoğan and oriented towards a more religious and nationalist political agenda.
Secret Structures and the Cold War.
The influence of shadow networks in Turkey foreshadowed developments spurred by the global tensions of the Cold War era.
The Cold War (1947–1991) spurred the expansion of security and intelligence structures in many states. The United States and the Soviet Union, along with their allied governments, spent a lot of money on intelligence, covert operations, and covert security networks. In the United States, a mass national security apparatus was established by the National Security Act of 1947, which created the CIA.
Operation Gladio was a secret network of resistance. Several NATO states organized it in case of a Soviet invasion of Western Europe. These so-called ‘stay-behind’ networks operated in Italy, Belgium, Turkey, Germany, and other countries and were officially meant to be activated only in wartime. Later evidence suggested involvement in peacetime political activity, including efforts to undermine left-wing groups and movements.
From a Turkish Concept to a Global Debate
From its Turkish origins, the idea of the deep state entered political discourse in other parts of the Middle East and South Asia. It then entered debates in Western democracies. The term passed from a primarily academic instrument to a highly loaded political term when political figures in the United States, particularly Donald Trump, began discussing the deep state in relation to resistance within the federal bureaucracy. As a result, public awareness of the term increased, but its meaning became more confused and more easily abused in political rhetoric.
The Deep State Comprised of What? Its Key Components
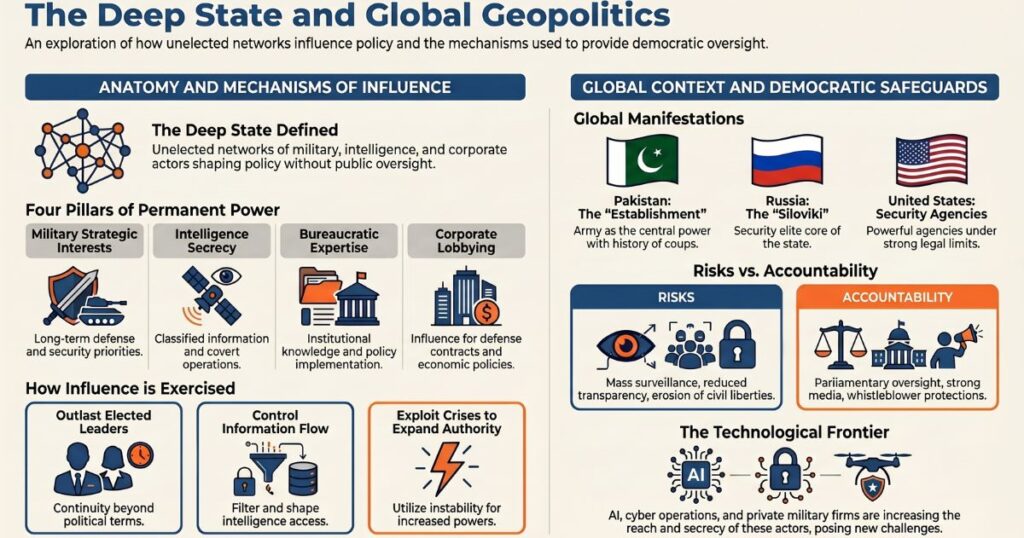
A. The Military Establishment
Military forces also have their own interests, ways of thinking, and long-term plans, which, in most cases, extend far beyond the reign of any elected government. This was cautioned against by former U.S. President Dwight D. Eisenhower, the Supreme Allied Commander during the Second World War, in his farewell address in January 1961. He referred to a military-industrial complex and warned that the united strength of the military and the defense industry could, unless it reined in, result in public policy serving them rather than the people. His worry has been applicable in most countries where military leaders shape defense budgets, strategic decisions, and even foreign policy in ways difficult for elected leaders to modify.
B. Intelligence Agencies
Intelligence services are the most confidential and least accountable aspect of a state’s power. They collect data, conduct undercover missions, and determine what to disclose to elected officials and what to conceal. Based on declassified documents from Lithuania, Moldova, and Poland, political scientist Suzanne Freeman demonstrates that even in authoritarian states, such agencies may possess clear foreign policy objectives. They can do so to advance those interests when they are not in line with the official state policy. Freeman outlines four primary approaches to changing the information sent out: distorting analysis to favor leaders, acting without authorization to alter facts on the ground, and coercing political leaders to do so.
C. The Permanent Bureaucracy
Career civil servants include lawyers, economists, diplomats, and administrators who are relied on by every state. They remain in their stations when the government changes, and they bear institutional memory and expertise. This provides them with actual power in the implementation of the laws and the formation of policies. In the United States, according to Francis Fukuyama, the so-called deep state is, in many cases, a professional civil service. To him, such a civil service is a necessary component of any working liberal democracy. This raises a critical issue of administrative continuity, not necessarily indicating a clandestine conspiracy. The major issue is whether civil servants are working within clear legal boundaries and democratic checks and balances, or whether they can use their offices to obstruct the decisions of elected leaders who have made legitimate decisions.
D. Corporate and Financial Networks.
Another level of long-term influence is established through the connection between the government and big corporations. It has been common practice in the military, intelligence services, and large corporations to exchange senior officials between posts. The big contractors like Lockheed Martin, Boeing, Raytheon, Northrop Grumman, and General Dynamicsalso spend huge sums lobbying and making campaign contributions, and employ numerous former senior officials. Financial institutions dealing with government debt or payments on behalf of defense programs are also important players. Such relationships help create networks that benefit from significant defense spending and consistent contracts and can influence policy in that vein.
E. Media and Information Systems.
One source of power is control over information. Propaganda and disinformation have long been in use by governments and security agencies. Such campaigns have become more sophisticated in recent years, thanks to new tools, and it is increasingly difficult for a common citizen to notice. An example is the Russian scheme of the Doppelganger, a 2025 report by the Canadian Digital Media Research Network, cited in an FBI affidavit. The actors associated with the Russian state created fake websites in this campaign to imitate the look of channels like Fox News, The Guardian, and Bild. They relied on these platforms to post fake news and to fuel tensions in Western societies. The case demonstrates how deep-state actors may use media systems and digital platforms to influence public debate without attracting public attention.
Case Studies: Deep State in Five Countries.
A. Turkey: The Model Case.
The country in which the deep state concept was first used in ordinary language and remains one of the most researched concepts is Turkey. Since the last years of the Ottoman Empire and the early years of the republic, scholars have noted a trend in which relationships among military personnel, intelligence agencies, nationalist paramilitaries, and criminal organizations are managed with either loose or partial control. Such networks have been attributed to the stifling of Kurdish political demands, the assassination of journalists, and, based on various investigations, the smuggling of heroin to finance operations that are not registered in the official budget.
In the late 2000s, with the Susurlu crash in 1996 and the Ergenekon trials, certain elements of this structure were brought to the surface, although it was not eliminated. Many of the Ergenekon convictions were overturned. Analysts believe that the system was not demolished but changed. With President Recep Tayyip Erdoğan and the Justice and Development Party (AKP), a deep state that had been linked to secular military elites was restructured to fit a more religious and nationalist agenda. The Turkish case implies that a deep state is not bound to a single ideology or party; it is an institution and networks that can be taken over and repurposed by new parties in power.
B. Pakistan: In the Land of the Army Making Limits.
One of the best examples of military dominance in a formal democracy is the deep state of Pakistan, commonly referred to as the Establishment. The army seized direct government control in 1958, 1977, and 1999 since gaining independence in 1947. During the interim coups, it has maintained a powerful role in decision-making, particularly in matters of security and foreign policy.
The outcome has been a weak democratic history. According to Al Jazeera and other media outlets, no civilian prime minister has served a full five-year term. Leaders who defied the army have been ousted or issued severe repercussions. In 1979, Zulfikar Ali Bhutto was toppled by General Zia-ul-Haq and hanged. In 2007, his daughter Benazir Bhutto was assassinated. Nawaz Sharif was ousted and exiled on several occasions. In 2023, relations with army leaders collapsed, and Imran Khan, who assumed power at least partially with military backing, was jailed on a number of charges.
According to Khawaja Asif, Pakistan’s defense minister in 2025, the nation operates under a hybrid system in which governance is shared jointly by civilian leaders and the army through a consensus process. According to critics, such a gracious expression of words conceals the fact that the military has a veto on fundamental policies and can prevent or overturn decisions it does not like. Armed proxies used by the security establishment have also gained wide publicity in the form of the Afghan Taliban, the Haqqani network, and other groups like the Lashkar-e-Taiba as instruments of regional policy, in Afghanistan and against India.
C. Egypt: The Military Economy within the State.
An example is seen in Egypt, where the military controls politics and much of the economy. The Egyptian Armed Forces (EAF) operates a business in the food production, construction, tourism, and manufacturing industries. According to scholars, this system is referred to as a state within a state, or an economy within an economy, and military-owned companies enjoy special benefits and lack transparency.
Another area in which the army has been involved is the political sphere, where its leaders perceived their status as in danger. General Abdel Fattah el-Sisi engineered a coup in July 2013 that toppled President Mohamed Morsi, who had been elected in 2012. El-Sisi subsequently became a presidential candidate and is still in office. In this respect, Egypt demonstrates how a deep state within an authoritarian system can be practically indistinguishable from the official state, a place where uniformed leaders and their economic connections are the central forces.
D. The United States: Power of Institution and Political Contention.
The situation in the United States is more complicated. It is well endowed with electoral and legal institutions, but it is also home to large intelligence agencies, a strong military, and a history of covert operations. When Donald Trump claimed that a deep state was opposed to his presidency, he cited the fact that permanent officials could oppose or slow certain of his policies. According to many scholars, such assertions were mostly overstated or a political weapon. According to UCLA law professor Jon Michaels, American power structures are nearly completely transparent compared to those of countries such as Egypt, Pakistan, or Turkey.
Nevertheless, there are some stark instances in which U.S. security agencies have exercised power in ways that raise deep-state concerns. The CIA assisted in arranging or sponsoring coups in other countries during the Cold War. In 2013, the revelations made by Edward Snowden revealed that the surveillance of digital communications carried out by the National Security Agency (NSA) included the data of ordinary citizens on a large scale. The misleading information before the Iraq invasion in 2003 on weapons of mass destruction also tarnished the trust of the people. This is why some analysts view the United States as a nation in which both perspectives are to some extent true: the permanent institutions are more stifled than in most other states, but their ability to operate with minimal control is a major problem.
E. Russia: The Security Services in Charge
To many observers in Russia, the deep state is virtually indistinguishable from the state. Siloviki are the present and former members of the security services and military who are at the heart of politics and business. Through President Vladimir Putin, this group controls major ministries, state enterprises, and intelligence groups. Mark Galeotti and other analysts believe that Russia keeps its key services, the Federal Security Service (FSB), the Foreign Intelligence Service (SVR), and the military intelligence service (GRU) on an all-volunteer war footing. The FSB, which is heir to the Soviet KGB, is reported to have close ties with organized crime groups as well.
The work of Suzanne Freeman supports the view that Putin is a representative of the institutional culture of the KGB and its heirs, not a separate one. His foreign policy decisions are consistent with traditional views of the security establishment, including being hard on NATO expansion and continuing to exert influence on former Soviet republics. In this regard, Russia can be used as an example of a deep state that has stepped out of the shadows and seized formal control of the whole political system.
A Tension of Baseness: The Deep State and Democracy.
A. The Threats of an Unaccountable Power.
Deep-state institutions are a threat to democratic governance. When the authority of elected officials in a government is undermined by unelected actors wielding decisive power to shape or influence important policies, the notion that governments derive their power from the consent of voters is compromised. In particular, the lack or minimal supervision of intelligence agencies is most likely to be abused, as their operations are not visible to the public.
Such powers were extended to the mass surveillance undertaken by the U.S. National Security Agency (NSA), which was exposed in 2013 by documents leaked by Edward Snowden and reported by publications such as The Guardian. These programs stored information on hundreds of millions of individuals, some of whom were not suspected of any kind of crime. This is an illustration of how the vast powers of national security, when not checked by robust legal and political restraints, may undermine civil liberties on a massive scale.
B. The Stability Argument
Advocates of robust permanent institutions have a different perspective. According to them, continuity, expertise, and simple stability are offered by professional bureaucracies, military staffs, and intelligence services. These institutions can guard against abrupt policy changes that could destabilize economies, alliances, or domestic security. It is also possible to use them as a check on leaders who may be tempted to bend the law or concentrate power in their own hands.
Once, MI6 chief John Sawers said the deep state is what keeps us stable. This remark reflects the view of most authorities that the persistence of institutions is critical to the success of government in complex societies. The main issue in this case is not to eliminate these institutions but to ensure that they operate under transparent democratic guidelines, with actual checks and balances and respect for human rights.
C. The Deep State and the State intersect in Authoritarian Systems.
The distinction between the deep state and the government is extremely narrow in places like Russia, Egypt, and, to a considerable degree, Pakistan. The military commands, the intelligence agencies, and other related economic networks are security institutions that do not just push elected leaders behind the scenes. They are usually the primary decision-makers, and the role of civilian politicians is rather limited or nominal.
When it comes to such systems, it is particularly challenging to speak about reforming the deep state. True reform would imply that the people who already possess the supreme power would be required to diminish their authority and turn to real control. The reality is that they are seldom motivated to do so. To political scholars, these cases present the most intractable variant of the deep state issue: when security agencies are so deeply embedded in the regime that genuine democratization would entail a complete reorganization of the state.
Transnational Deep State Networks: Power without Borders.
A. A Shared Intelligence System: The Five Eyes.
The Five Eyes alliance, a signals intelligence alliance between the United States, the United Kingdom, Canada, Australia, and New Zealand, is one of the most obvious examples of a transnational security network. The alliance was a result of collaboration between British and American code-breakers in Bletchley Park during the Second World War. It was codified in the secret UKUSA Agreement of 5 March 1946, and subsequently in Canada in 1948, and in Australia and New Zealand by the mid-1950s.
The alliance today operates by coordination of national agencies: the NSA in the United States, GCHQ in the United Kingdom, the ASD in Australia, CSE in Canada, and GCSB in New Zealand. They have a worldwide network of intercepting communications together with undersea cable taps, satellite listening stations, and centers of cyber operations. The Five Eyes were described by former NSA contractor Edward Snowden as a supranational intelligence agency not accountable to the established laws of the respective countries. In 2013, his leaks revealed that these services were sharing information about citizens with one another, which critics have argued facilitates bypassing domestic surveillance restrictions by sending requests to partner agencies.
B. Military Alliances and Shared Command Structures
Another level of transnational security power is generated by defense alliances. An example is NATO, which unites armed forces, intelligence agencies, and planning staffs of most member states under common command structures. Alliance frameworks are characterized by extensive strategic doctrines, joint exercises, and procurement decisions being discussed and agreed upon. National parliaments may have accepted general commitments, but they usually do not have direct authority over many of the specific operational and intelligence-sharing arrangements.
NATO is not the only ones that follow these patterns. Other regional and bilateral defense alliances connect armies and security agencies, influencing their information collection, operational planning, and weapon acquisition. In practice, it implies that certain key decisions regarding war, peace, and surveillance are made in forums that are partially outside the usual national democratic procedures.
C. Global Capital and Corporate Influence.
Multinational corporations provide another layer of transnational deep-state action. Big US and European defense companies have ties to governments in most areas. Lockheed Martin, Boeing, Raytheon, Northrop Grumman, and General Dynamics have paid big money in lobbying and campaign finance in the United States and have good business relationships elsewhere. Their business models are based on elevated and consistent defense expenditures.
Another factor involves financial institutions when they handle government borrowing, facilitate large arms sales, or make payments on large defense contracts. These economic actors tend to develop an interest in the persistence of military activity and in some forms of alliances. This means that corporate and financial networks can support the popularity of security institutions and complicate elected leaders’ ability to cut budgets and/or alter strategy, even when a population shifts its views.
When Analysis Becomes Conspiracy Theory: The Menaces of the Deep State Concept.
A. Idea to Weapon.
Serious scholarship has employed the concept of the deep state, though it has also been employed as a political term to refer to those who disagree. Politicians and commentators occasionally use the term deep state to imply that any opposition within the bureaucracy is unacceptable. The term is not applied to comprehend the actual institutions but rather to discredit judges, civil servants, or journalists who challenge those in power.
Proponents of Donald Trump in America, as an illustration, argued that there was some kind of undercover club of liberal officials that was acting in an organized manner in order to prevent a conservative government. The same phrase has been used in speeches of other leaders where the undefined deep state forces, usually associated with foreigners, are accused by them of plotting against them. Such applications of the term are not generally based on solid evidence regarding real structures or decisions. They are urging citizens to view any failure as a sign of a dark conspiracy rather than a natural part of political conflict.
Building on this politicization, the QAnon movement in the United States exemplifies how deep state rhetoric merges with conspiracy theories. During 2017-2021, QAnon supporters promoted the idea of a secret group of elites- politicians, business leaders, and celebrities- controlling world events through criminal schemes. Investigators from journalism, academia, and law enforcement dismissed these claims due to a lack of evidence.
The QAnon movement in the United States demonstrates the integration of deep-state language into a broad range of conspiracies. During 2017-2021, QAnon supporters advanced the notion that a covert organization of influential people- politicians, business executives, and celebrities- was operating a child-pornography ring and manipulating the world. Researchers, journalists, and law enforcement groups that investigated these claims rejected them as lacking a factual basis.
QAnon exemplifies a trend in which the deep state is a catch-all foe. Any information that contradicts the theory is considered a cover-up. Within such a closed system, the concept ceases to be an instrument of cautious study and instead promotes a worldview in which normal democratic debate and institutions are perceived as parodies or as dominated.
C. What the Academics have to say about the Conceptual Frontiers.
Some scholars have expressed objections to the concept of the deep state. People complain that it lacks clear demarcation and is thus difficult to use consistently, and that it bends to suit past beliefs. Abdelwahab El-Affendi, in an article for the Doha Institute, argues that the term tends to reflect ideological differences rather than offer a valid description. He refers to this tendency as The Fantasy of the Deep State and cautions that applying this approach in political science may be the overflow of propaganda into academic writing.
These are some of the criticisms that identify a significant work of students and researchers. Instead of dismissing the concept, they may apply it with high standards: requiring strong evidence, distinguishing documented institutional practices from speculative ones, and watching for the possibility of slipping into conspiracy theory. In this manner, deep state analysis may help explain actual trends in power without making every political outcome a conspiracy.
Future and New Technologies and the Hidden Power.
A. Mass Surveillance and Artificial Intelligence.
The latest developments in artificial intelligence are altering states’ surveillance capabilities. AI systems can analyze and discern trends in the actions of large groups of people and prioritize individuals or groups of interest to further scrutiny with minimal human oversight. This reduces monitoring costs and makes it easier for security agencies to monitor people in real time.
Critics such as Edward Snowden have cautioned that governments can use AI-enhanced surveillance not solely to combat terrorism or serious crime, but to regulate the overall social behavior. Self-censorship and obedience can be facilitated by the knowledge that any communication, movements, and internet interactions can be analysed in real time. By doing so, AI technologies can be used to empower deep-state actors who seek to increase surveillance and control without debate in society.
B. Cyber Operations as a Routine Statecraft.
The war in Ukraine demonstrates that cyber operations and information campaigns can be combined with conventional military force in the same plan. Critical infrastructure, including power grids, hospitals, and financial systems, has been targeted by state-linked hackers, and organized online campaigns attempt to sway opinion both domestically and internationally. Governments in Russia, China, Iran, and North Korea have been associated with similar activities.
These activities are usually conducted by departments within intelligence services or military cyber organizations, which are run in a low-profile manner. They tend to fall below the legal threshold for war, making them more difficult to regulate under current international law. Consequently, cyber operations have emerged as a common tool among deep-state actors seeking to gain an advantage in the grey zone between open conflict and declared peace.
C. Private Military and Intelligence Contractors.
Another significant development is the expanded use of private companies to perform tasks once reserved for regular armed forces and state intelligence agencies. Other US contractors like the American Blackwater (which was later renamed Academy) were very active in Iraq and Afghanistan, providing some of the armed protection, training, and logistical support. By 2006, there had been more private contractors in Iraq than uniformed U.S. soldiers there.
The Russian Wagner Group has been active in Ukraine and Syria, as well as in several African nations, providing combat services, training, and protection to governments and resource projects. These companies tend to operate either under government direction or with government permission but are not part of ordinary military chains of command. This arrangement facilitates moving fighters across borders, allows states to distance themselves from alleged atrocities, and keeps many operational details secret. In practice, private military and intelligence contractors expand the deep state’s power and make it less accountable.
D. The Issue of International Accountability.
National oversight structures are unable to keep pace with the increased use of cross-border digital networks, multinational corporations, and deep-state security partnerships. Parliaments can at least question their own heads of intelligence, and examine the laws of their own countries. They possess far less direct control over overseas agencies that exchange data, privately operated platforms that carry out vital functions, or coalition military set-ups that coordinate combined operations.
This is a gap that poses challenging questions. Who checks collaboration within alliances (like the Five Eyes or NATO) with regard to monitoring and covert action? What can citizens do to hold multinational contractors accountable who simultaneously act in multiple jurisdictions? These concerns imply that new legal mechanisms and modes of public oversight will be needed to manage deep-state power in the future, commensurate with the transnational complexity of contemporary security and technology.
Reform and Accountability: Can Change Be Had?
Democratic Checks and Balances.
Oversight bodies are the primary formal mechanisms of checks and balances in democratic systems that ensure that deep state actors are kept in check. These include parliamentary or congressional intelligence committees, independent courts to review security measures, and inspector general offices to investigate malpractice within agencies. With sufficient legal mandate, technical skills, and political goodwill, these institutions can check abuses and ensure that security services adhere to the law.
In practice, they are inclined to encounter impediments. Lawmakers might not have access to classified data or can rely on the agencies that they are supposed to investigate. Judges tend to hesitate to question national security claims. Inspectors general can have their mandates or budgets reduced. Consequently, supervision is at times on paper rather than in practice.
Whistleblower Laws and Protection.
The availability of information legislation and well-furnished safeguards for whistleblowers are fundamental components of any endeavor to restrain obscure influence. Freedom of information systems enables journalists, researchers, and ordinary citizens to request documents and information about government operations, even after they are declassified. These laws can uncover missed or overlooked patterns when used properly by oversight bodies.
Most of the key exposures of deep-state actions have come from people within the system who have opted to blow the whistle. The Pentagon Papers about the Vietnam War, CIA torture, and secret detention camps, and the revelations of NSA surveillance programs revealed by Edward Snowden are some examples. These were individuals who involved themselves in grave personal dangers. Their right to legal protection is relevant both to protect them against retaliation and to indicate to the state that they are open to external scrutiny as part of democratic life.
International Law and Human Rights Standards.
Another set of tools is provided by international human rights law, but it is usually more difficult to implement. Norms on privacy, due process, and surveillance and detention limits are outlined in treaties such as the International Covenant on Civil and Political Rights and in guidelines formulated by the United Nations and regional bodies. These standards are at times used by civil society organizations, courts, and international organizations to question abusive practices.
But strong states can defy or disregard such pressure, while weak states may lack the ability to carry out reforms even when they agree in principle. In many cases, security agencies are adept at making their actions appear in the name of national defense, thereby minimizing political scrutiny. This means that while international norms matter, they rarely bring about change unless domestic actors—legislators, judges, media, and social movements—are willing to use them to push for concrete limits on deep-state power.
Conclusion: Living with Hidden Power in a Democratic Age
Deep state structures are real features of modern politics. Military organizations, intelligence services, permanent bureaucracies, and major defense contractorsall exercise significant influence in every state. In some countries, these actors operate within meaningful legal and democratic limits. In others, they have come to dominate public life and weaken, or almost replace, elected institutions. For students of politics, international relations, and human rights, understanding these differences is essential.
Meanwhile, the deep state does not consist of a single secret committee that straightforwardly coordinates events. It can be more appropriately described as a battery of long-standing networks, professional interests, permanent institutions, and secret or classified information that influence long-term decisions. These forces are sometimes extremely difficult to observe, and they tend to operate through ordinary processes rather than melodramatic intrigues. The assignment is to read them with evidence and clarity of ideas, with due caution and careful comparison, without reducing every political development to evidence of some mysterious design.
The work is more urgent due to new technologies. Artificial intelligence, cyber activity, and worldwide transfers of individual capital enable security organizations and their agents to track, manipulate, and exert power less publicly than in the past. Surveillance that once required large physical systems can now be carried out through software and consumer devices. Information campaigns can target individuals and groups directly on digital platforms. Private military firms can move personnel and equipment across borders under commercial cover.
In this environment, democratic societies face difficult questions. How can they gain the benefits of expert, stable institutions while still keeping those institutions under real public control? What forms of oversight, transparency, and law are needed when security work is deeply integrated into global networks? The answer will not come from simple slogans or from denying that hidden power exists. It will depend on patient analysis, informed public debate, and political choices that treat accountability as a central part of security policy rather than an optional extra.
Sources:
Demiroz, F. (2025). The Origins and Intellectual Structure of the Deep State Literature. Public Administration Review, 85, 1666-1681.
Hovhannisyan, H. (2025). The Deep State in Turkish Politics: Historical Roots and Contemporary Transformations. Analytical Bulletin.
O’Neil, P. H. The Deep State: An Emerging Concept in Comparative Politics.
Freeman, S. (2025). The Shadow Architects of Power. MIT Department of Political Science.
Mills, C. W. (1956). The Power Elite. Oxford University Press.
Yu, Z. (2026). Reform of the American Bureaucratic System from the Perspective of the “Deep State” Theory. ICHESS 2025.
Galeotti, M., et al. (2025). Siloviki. Russian Analytical Digest, No. 323. Center for Security Studies, ETH Zürich.
Subramanian, A. (2025). Pakistan’s politico-military tango: Relationship fractured by deep State. Hindustan Times.
Mason, C. (2024). The American Deep State: Balancing Effective Government with Democratic Accountability. PA TIMES Online.
Kolga, M., et al. (2025). Kremlin Doppelgänger Tactics and the Exploitation of the Charlie Kirk Murder. Canadian Digital Media Research Network.
Gerecht, R. M. (2025). There Is No Deep State. The Dispatch/FDD.
El-Affendi, A. (2019). The Fantasy of the ‘Deep State’: The Spillover of Propaganda into Political Science. Doha Institute.